12 mins
Colocation for Healthcare: HIPAA-Compliant Infrastructure for Hospitals, Health Systems, and Clinical IT Teams
Healthcare colocation means housing a hospital or health system's own servers in a third-party data center that provides the physical security, redundant power, and compliance documentation that the Health Insurance Portability and Accountability Act requires and that most internal server rooms cannot deliver. Health systems choose colocation over cloud, bare metal hosting, or VPS for ePHI workloads because it combines full hardware ownership with professionally managed, audit-ready infrastructure.

It is 2:17 in the morning. A ransomware payload that entered through a phishing email six weeks ago has just activated across your hospital's network. The EHR goes dark. Nurses are switching to paper. The ED is diverting ambulances. Radiology cannot pull images. In the next 45 minutes, your infrastructure team will make a series of decisions that your organization's legal, compliance, and clinical leadership will scrutinize for the next 18 months.
Whether those decisions lead to a full recovery in hours or a weeks-long operational crisis depends almost entirely on choices made long before tonight. Where is the ePHI stored? Is there a geographically separated recovery site? Does the colocation provider have an executed BAA? Are the access logs documented in a format OCR will accept?
Healthcare infrastructure is clinical infrastructure. Patient information, data protection, and clinical continuity all depend on the same underlying decision. This guide is for the IT directors, VPs of Infrastructure, and CIOs who are making it.
Colocation vs. Bare Metal vs. VPS vs. Cloud: What Healthcare Organizations Are Actually Choosing Between
Healthcare organizations evaluating infrastructure options in 2025 and 2026 are choosing between four categories of data center provider and service providers, each with meaningfully different tradeoffs on compliance documentation, cost predictability, control, and clinical performance: colocation, dedicated bare metal hosting, virtual private servers, and public cloud.
Colocation means your organization owns and manages its own servers, housed in a third-party data center that provides the physical facility, power, cooling, physical security, and network connectivity. You bring your own hardware. The facility provides everything around it. For healthcare, colocation is the model that gives the most complete control over ePHI while still delivering professionally managed infrastructure. It is also cost efficient compared to building and maintaining an in house data center that meets current HIPAA, HITECH, and SOC 2 standards.
Dedicated bare metal hosting means a provider owns the physical server hardware and leases it exclusively to your organization. You get dedicated resources without multi-tenancy risk, but the hardware is theirs. For healthcare buyers evaluating bare metal hosting, the key question is whether the provider executes a BAA and whether the physical facility holding those servers meets HIPAA physical safeguard requirements. Many bare metal hosting providers are not equipped to answer that question.
VPS (virtual private server) hosting places your workloads on shared physical hardware with logical isolation. The cost is lower but the security boundary is a software construct rather than a physical one. For general administrative workloads with no ePHI, VPS may be acceptable. For clinical systems, EHR environments, and any workload touching electronic PHI, VPS introduces shared infrastructure risk and lacks the physical security measures that most healthcare compliance programs require.
Public cloud (AWS, Azure, Google Cloud) offers scalability and a path to BAA execution through each major provider's healthcare compliance programs. For development, analytics, and non-ePHI workloads, cloud is a strong fit. For production EHR hosting, real-time clinical applications, and workloads where data residency documentation is a regulatory requirement, cloud introduces complexity around HIPAA physical safeguard attestation, egress costs, and latency that many health systems are now actively managing by moving production workloads back to colocation. More on that below.
Option | Hardware ownership | PHI control | BAA availability | HIPAA physical safeguard documentation |
Colocation | You own the hardware. | Full, subject to your controls and the facility’s access/security procedures. | Often available from healthcare-grade providers, but not universal. | Strongest when the provider supplies access logs, facility controls, and audit support. |
Bare metal hosting | Dedicated physical hardware; ownership varies by provider. | High, because the hardware is dedicated and not shared via virtualization. | Varies significantly by provider. | Depends on the provider’s facility and operational documentation. |
VPS | Shared physical host, logically isolated. | Moderate to limited, because control is virtual rather than physical. | Often available, but it does not eliminate the physical-separation issue. | Harder to map to physical safeguards because the underlying hardware is shared. |
Public cloud | Provider owns and operates the infrastructure. | Indirect; customer configures workloads and remains responsible for HIPAA usage decisions. | Available from AWS, Azure, and GCP under BAA programs. | Supported through provider reports and shared responsibility documentation, but you still need your own risk analysis. |
Find the Right Infrastructure for Your Healthcare Workload in 5 Minutes
For buyers who are not sure whether colocation, bare metal, vps or cloud will be a better fit, Inflect built this quick decision tool drawing on data from global top-tier providers, real-world industry use cases, and expert advisory recommendations, to help buyers cut through the noise and identify the right infrastructure model for their specific situation.
—> Help me find whether colocation, bare metal, vps, or cloud will be the right fit
Why Healthcare Organizations Are Moving Clinical Workloads Out of Public Cloud
Healthcare organizations are increasingly moving production clinical workloads from public cloud back to colocation for four reasons: unpredictable cost at scale, data residency and audit documentation complexity, EHR latency requirements that cloud environments struggle to meet consistently, and compliance posture gaps that emerge during OCR investigations and cyber insurance renewals. The HIPAA Omnibus Rule, which expanded the administrative safeguards and technical safeguards obligations to business associates and their subcontractors, has made the documentation chain more complex in cloud environments where physical infrastructure ownership is several layers removed from the covered entity.
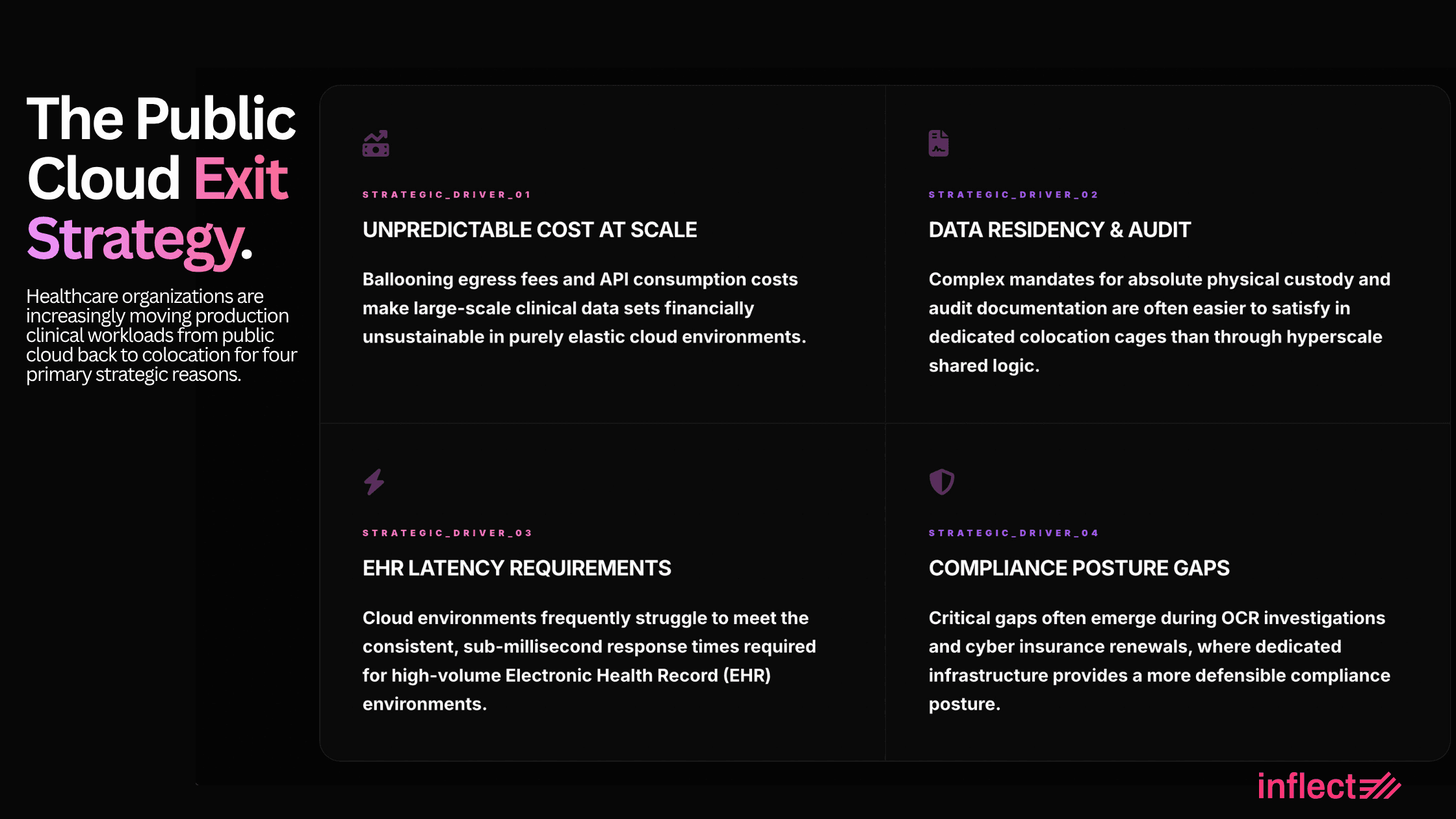
1. Cost predictability
Cloud costs for healthcare workloads scale with data volume, and healthcare generates significant data volume. Medical imaging files, long-term records retention, real-time monitoring streams, and high-transaction EHR environments all generate egress charges, storage costs, and compute bills that compound in ways that healthcare IT budgets did not initially model. Health systems that moved to cloud in 2019 or 2020 are now doing cost optimization analyses that consistently show production EHR and imaging workloads run materially cheaper in colocation over a three-year horizon.
2. HIPAA documentation chain
HIPAA's Security Rule requires covered entities to document their risk analysis, physical safeguards, and audit controls in ways that OCR investigators can evaluate. In a colocation environment, the health system owns the hardware, holds the BAA with the facility, and can produce access logs, physical security documentation, and risk analysis evidence that is directly attributable to their own infrastructure. In a cloud environment, the physical safeguard documentation runs through the cloud provider's own compliance reports (SOC 2, ISO 27001), which OCR accepts but which require the health system to maintain a layer of translation between what the cloud provider documents and what the health system's own risk analysis covers. That translation gap becomes visible during investigations.
3. EHR performance
Epic, Oracle Health, and athenahealth implementations are transaction-intensive systems where storage I/O and network round-trip latency directly affect clinician workflow speed. Colocation in a facility with direct fiber connectivity to the health system's clinical sites, sub-5ms latency to major carriers, and dedicated storage infrastructure consistently outperforms general-purpose cloud environments for EHR transaction workloads. The performance difference is measurable in page load times and becomes operationally significant across thousands of daily clinical interactions.
4. Cyber insurance requirements
Healthcare cyber insurance underwriters are increasingly asking for specific evidence of physical infrastructure controls, network segmentation documentation, and audit trail capabilities that colocation environments document more directly than cloud environments. The combination of a SOC 2 Type II report from the colocation facility and the health system's own BAA and risk analysis documentation satisfies underwriter requirements more cleanly than the equivalent cloud compliance documentation chain.
Self-Managed Bare Metal in Colocation: Full Control Without the Facility Overhead
A growing number of health systems and healthcare IT organizations are choosing a specific colocation model that competitors rarely discuss: colocating multiple dedicated bare metal servers in a carrier-neutral facility, then managing those servers entirely in-house without any provider-managed services layer.
This model is specifically attractive to health systems that have experienced the security and compliance risks of multi-tenant environments, want zero shared infrastructure for ePHI workloads, and have the internal IT capability to manage a server fleet but do not want the overhead of owning and operating a physical data center facility. The facility provides power, cooling, physical security, network connectivity, and compliance documentation. The health system owns and manages every server in the cage.
The operational profile looks like a private data center but without the capital expenditure of land, construction, facilities management, and environmental systems. Health systems using this model typically deploy 10 to 50 physical servers in a dedicated cage, connect to multiple carriers for redundant network paths, manage their own hypervisor layer, and maintain direct physical access to hardware for maintenance and replacement. The colocation facility's BAA covers the physical environment; the health system's own security controls cover everything above the physical layer.
For organizations running large PACS archives, population health analytics platforms, or custom AI inference workloads that require specific hardware configurations not available in cloud or managed hosting environments, self-managed bare metal in colocation is frequently the most cost-effective and compliance-sound infrastructure model available.
What HIPAA Actually Requires from a Colocation Facility
Healthcare colocation providers must satisfy five specific HIPAA Security Rule requirements that impose obligations on the physical facility itself, confirming the data center adheres to standards far beyond standard enterprise compliance: physical safeguards, audit controls, contingency planning documentation, a signed business associate agreement, and incident notification procedures meeting HITECH breach notification timelines. HIPAA compliance is not a certification achieved once. It is a continuous process of risk analysis, documented controls, and audit readiness that a colocation provider serving healthcare must support as an ongoing operational commitment.
1. Physical safeguards
Physical safeguards require documented facility access controls, workstation security policies, and physical protection for devices storing ePHI. For a colocation provider, these security measures mean biometric entry systems, 24/7 on-site security personnel, individual locked cages or cabinets for each tenant, video surveillance with documented retention periods, and visitor escort procedures. Across all data center facilities serving healthcare clients, these controls must appear in the provider's SOC 2 Type II report, not just in marketing materials.
2. Audit controls
Audit controls require hardware, software, and procedural mechanisms that record and examine activity in systems containing ePHI. In a colocation environment, the facility must maintain granular physical access logs showing who entered which area, when, and under what authorization, and must produce these logs to support OCR investigations or internal compliance audits within a defined service level timeframe.
3. Contingency planning
Contingency planning under the HIPAA Security Rule requires covered entities to maintain data backup, disaster recovery, and emergency mode operation plans. The colocation provider's own business continuity plan, generator fuel supply, mean time to repair for power and cooling failures, and data access procedures during a disaster become part of the health system's HIPAA contingency planning evidence. Ask for the provider's own BCP documentation before signing.
4. Business associate agreement
Any colocation provider with physical access to servers storing ePHI is a business associate under HIPAA. A signed BAA is not optional. The BAA must specify the provider's permitted access, security obligations, and breach notification timeline. The BAA is the legal mechanism that binds the colocation provider to HIPAA's requirements for data integrity, patient information protection, and breach response. Providers that cannot provide a HIPAA-compliant BAA should be disqualified, because HHS requires a BAA whenever a cloud service provider creates, receives, maintains, or transmits ePHI on behalf of a covered entity or business associate. That requirement matters in a sector where healthcare continues to post the highest breach costs, with IBM’s 2024 reporting placing average healthcare breach costs at roughly $9.77 million to $10.93 million depending on the summary cited (HIPPA Journal, 2024).
5. Incident notification
The colocation provider's obligation to notify the health system of any physical security event, system anomaly, or environmental incident directly affects the health system's ability to meet HITECH's 60-day breach notification requirement. 2024 was one of OCR’s most active HIPAA enforcement years, with numerous resolution agreements and civil money penalties, including a $4.75 million settlement related to a malicious insider cybersecurity incident at Montefiore Medical Center. The incident notification timeline and escalation path should be specified in the contract rather than left to the provider’s discretion (Legal Health, 2024, Krieg Devault, 2025) .
Top Healthcare Colocation Use Cases
Healthcare organizations use data center colocation across five distinct deployment contexts, each requiring HIPAA-compliant data handling, different performance specifications, and different connectivity requirements: disaster recovery and business continuity, HIPAA-compliant ePHI hosting, hybrid cloud and cloud interconnection, high availability for clinical applications, and data-intensive workloads including imaging and population health analytics.
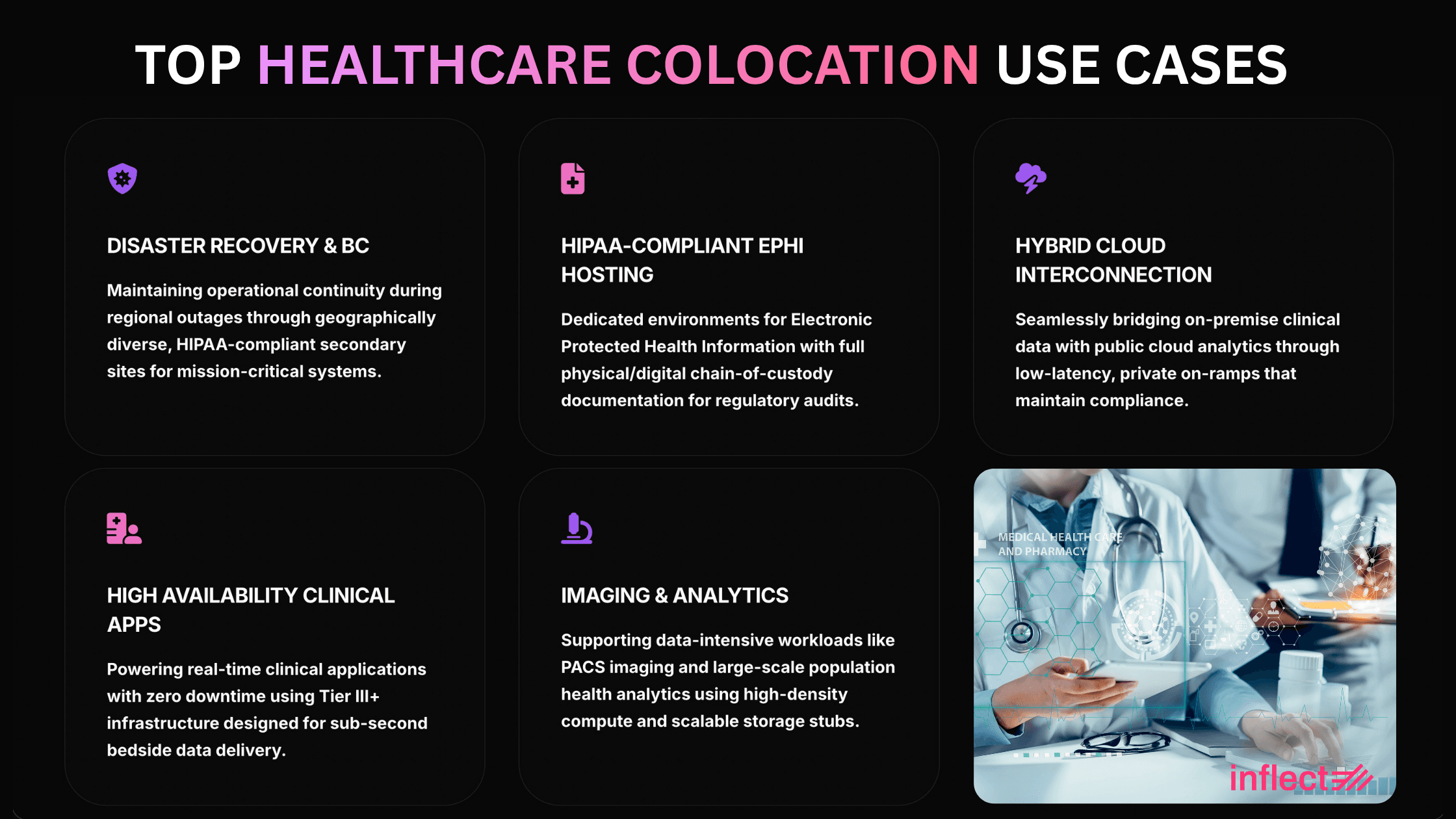
1. Disaster Recovery and Business Continuity
A geographically separated DR site in a colocation facility is the most common healthcare colocation deployment, satisfying HIPAA's contingency planning requirement while providing the operational failover capability that ransomware incidents, power events, and natural disasters require. Healthcare DR colocation covers EHR failover, secure data storage and backup, application recovery for clinical and administrative systems, continuous monitoring of replication health, and emergency access to ePHI when the primary facility is unavailable. The secondary colocation facility must be at least 100 miles from the primary site to avoid single-event failure scenarios, and it must execute its own BAA because it will process the same ePHI during a failover event. For health systems where the primary infrastructure is on-premises, colocation DR is often the first and most justifiable colocation investment.
2. HIPAA-Compliant Hosting for EHR and ePHI
Health systems, EHR vendors, and healthcare IT organizations colocate servers containing ePHI in professionally managed facilities that provide the physical security, access controls, environmental monitoring, and documentation that small on-premises server rooms and hospital data closets cannot match. This use case covers production EHR hosting, claims and billing system hosting, patient portal infrastructure, and long-term records retention. The facility's physical security documentation, access logs, and SOC 2 Type II report become part of the health system's HIPAA compliance evidence, reducing the internal documentation burden for physical safeguard requirements significantly.
3. Hybrid Cloud and Cloud Interconnection
Colocation serves as a secure bridge between on-premises healthcare systems and cloud platforms, allowing health systems to connect private clinical infrastructure to cloud services for analytics, backup, application modernization, and AI workloads without exposing core EHR systems directly to the public internet. Carrier-neutral colocation facilities with direct cloud on-ramps to AWS, Azure, and Google Cloud provide low-latency, private connectivity to cloud environments that is materially more secure and performant than routing the same traffic over standard internet connections. For health systems executing phased cloud migration strategies, colocation provides the interconnection hub that makes hybrid architecture practical.
4. High Availability for Clinical Applications
EHR platforms, pharmacy systems, practice management applications, patient portals, and clinical decision support tools require continuous uptime across clinical and administrative shifts. A colocation facility with redundant power feeds, N+1 cooling, generator backup, and 99.999% uptime SLAs provides the operational resilience that most internal server rooms cannot sustain. For health systems where a single power event or cooling failure would take down clinical applications, moving those workloads to a Tier III or Tier IV colocation facility eliminates the single points of failure that on-premises environments accumulate over time. AHA/Sg2 projects continued growth in outpatient, ambulatory, and virtual care over the next decade, which makes always-on connectivity and application availability a clinical requirement rather than just an IT preference (AHA, 2026).
5. Data-Intensive Workloads: PACS (Picture Archiving and Communication System ), Imaging, and Population Health
Medical imaging archives (PACS), radiology workstations, genomics data platforms, and population health analytics environments all generate data volumes and compute requirements that exceed what aging on-premises infrastructure supports. Colocation provides the additional storage capacity, higher power density, and network diversity that these workloads require without forcing a full cloud migration of regulated clinical data. Health systems running PACS in colocation benefit from the proximity to high-bandwidth carrier connections for fast image retrieval across clinical sites, and from the physical security documentation that supports HIPAA compliance for imaging data.
What Healthcare Buyers Must Evaluate in a Colocation Provider
A genuinely HIPAA-capable data center provider demonstrates six capabilities that separate healthcare-grade facilities from general enterprise data centers that claim HIPAA certification or compliance readiness without the depth to back it up: BAA execution with healthcare-specific terms, SOC 2 Type II certification scoped to the specific facility, physical access controls meeting HIPAA physical safeguard standards, uptime SLAs of 99.999% or better with documented financial remedies, healthcare network and payer connectivity, and a compliance support team experienced in OCR investigation response.
BAA execution: The provider must execute a HIPAA-specific BAA that defines their obligations, breach notification timelines shorter than 60 days, and their permitted access to ePHI. A standard data processing agreement is not a BAA.
SOC 2 Type II (not Type I): Type II covers controls operating effectively over time. Confirm the scope includes the specific hall and cage where your infrastructure will be housed, not just the corporate entity.
ISO 27001: Increasingly required for enterprise healthcare vendor qualification and cyber insurance purposes.
Physical access controls: Biometric entry, 24/7 on-site security staff, individual cage locking, video surveillance with documented retention, visitor escort procedures. All must appear in the SOC 2 report. (Check all security features for colocation on Inflect Data Center Colocation Map)
Uptime SLAs by component: Separate SLAs for power, cooling, and network. A combined uptime SLA that blends these three may obscure gaps. Ask for generator runtime, fuel supply agreements, and MTTR commitments in writing.
Audit log production: Confirm the retention period, format, and service level for producing physical access logs when requested. This is a service, not a self-service export. Healthcare buyers should model this against OCR investigation timelines.
Recommend reading: HIPAA Compliant Colocation Services for Hospitals: 2026 Buyer’s Guide
How to Source HIPAA-Compliant Healthcare Colocation
Inflect is a digital infrastructure marketplace and advisory platform where healthcare organizations, EHR vendors, and health system IT teams can source and compare HIPAA-compliant colocation providers across primary, secondary, and tertiary US markets, with filters for BAA execution capability, SOC 2 Type II and ISO 27001 certification status, physical security specifications, uptime SLA tier, healthcare network connectivity, and power density for clinical AI and imaging workloads.
Healthcare IT teams use Inflect to evaluate multiple qualified colocation providers simultaneously rather than running sequential RFP cycles that take months. The advisory team works directly with health system IT directors and compliance officers on HIPAA-specific requirements documentation, BAA review, provider evaluation criteria, and contract term negotiation. Whether you are sourcing initial colocation for an EHR migration, adding a HIPAA-compliant DR site in a secondary market, or evaluating providers for self-managed bare metal infrastructure for clinical AI or PACS workloads, Inflect provides the market access and advisory support that healthcare procurement requires.
Source HIPAA-Compliant Healthcare Colocation on Inflect Compare colocation providers on BAA execution, SOC 2 Type II certification, physical access controls, uptime SLAs, and healthcare network connectivity. EHR hosting, disaster recovery, imaging infrastructure, and hybrid cloud connectivity across primary and secondary global markets. Expert advisory support for HIPAA-specific requirements and contract negotiation.
→ Source Healthcare Colocation on Inflect
Not sure which solution is the best fit?
About the Author
Chanyu Kuo
Director of Marketing at Inflect
Chanyu is a creative and data-driven marketing leader with over 10 years of experience, especially in the tech and cloud industry, helping businesses establish strong digital presence, drive growth, and stand out from the competition. Chanyu holds an MS in Marketing from the University of Strathclyde and specializes in effective content marketing, lead generation, and strategic digital growth in the digital infrastructure space.
Contact:
Email:

